Common Cloud Security Gaps Organizations Often Overlook - Download
This resource is our most common findings after we've completed a cloud security assessment for an organization that is using M365 or Google Workspace. Use this guide, along with some of our other free resources to help enhance your organizations cybersecurity posture.
Organizations rely heavily on Microsoft 365 and Google Workspace for email, identity management, file sharing, and collaboration. While these platforms improve productivity and remote access, many environments gradually accumulate inconsistent security policies, excessive permissions, unmanaged third-party integrations, and underutilized security controls that can increase organizational risk. This resource explains how independent Microsoft 365 and Google Workspace security assessments help organizations identify misconfigurations, strengthen identity security, and improve visibility into cloud collaboration risks attackers commonly target.
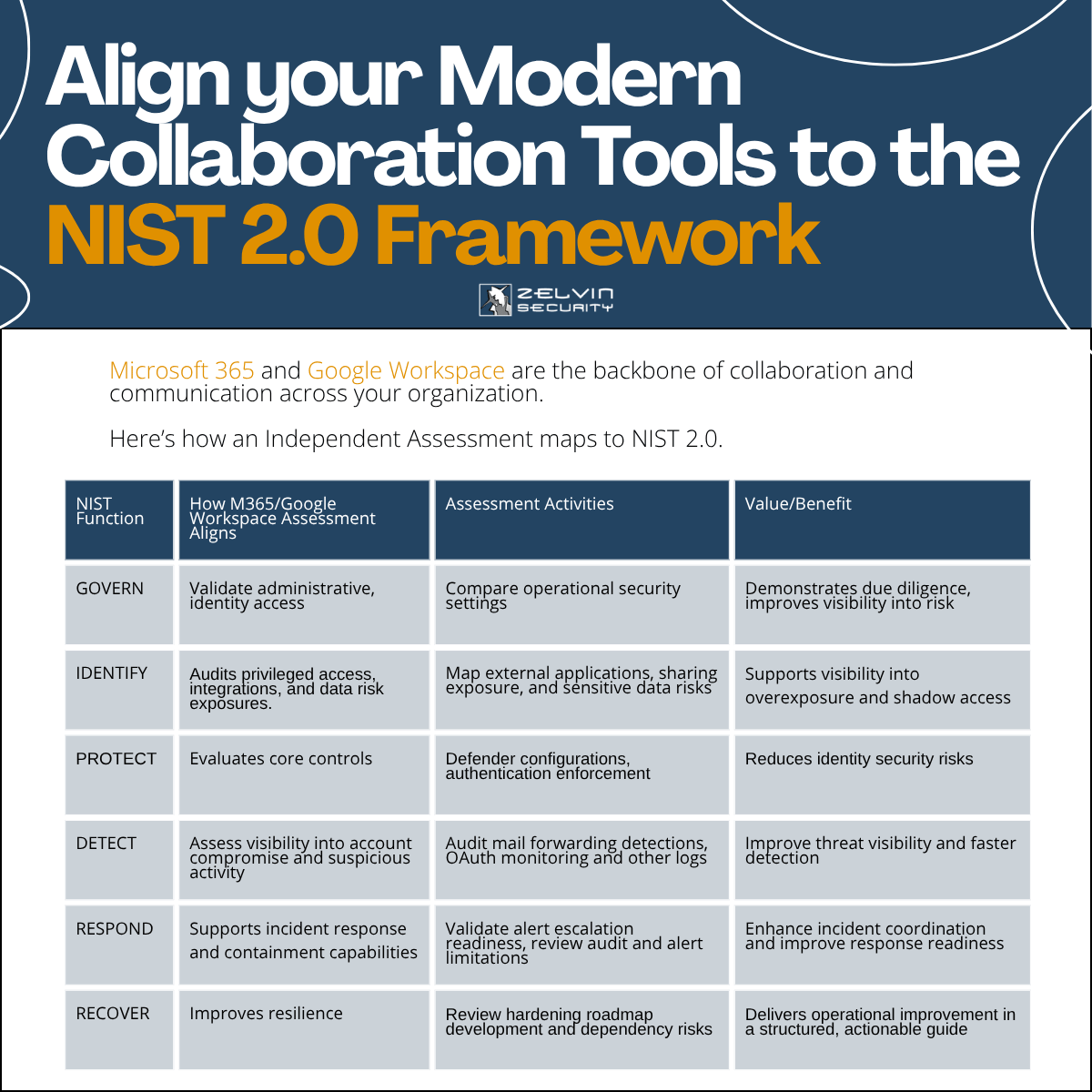
For IT Directors, CISOs, System Administrators, and security leadership teams, this guide provides practical insight into common cloud collaboration security challenges. It explores risks such as weak MFA enforcement, risky OAuth application access, excessive administrative privileges, insecure sharing settings, and gaps in monitoring or alerting capabilities. The resource also explains how cloud security assessments can support broader cybersecurity initiatives tied to NIST CSF 2.0, cyber insurance reviews, and organizational risk management programs.
This resource is designed for organizations looking to better understand how their Microsoft 365 or Google Workspace environment may perform under real-world attack scenarios. Rather than focusing only on compliance checklists or default platform settings, the guide explains how independent third-party security assessments provide evidence-based visibility into identity security, governance maturity, and cloud configuration risks. For organizations researching Microsoft 365 security assessments, Google Workspace security reviews, or cloud collaboration security best practices, this resource offers actionable insight to help leadership teams make informed cybersecurity decisions.
Make sure to read our article to go more in depth on this.
Download the resource by submitting the form.